Agentless vulnerability management to secure your Cloud Workloads
Discover vulnerabilities across your entire cloud infrastructure without installing any agent
Built by the team that has helped secure






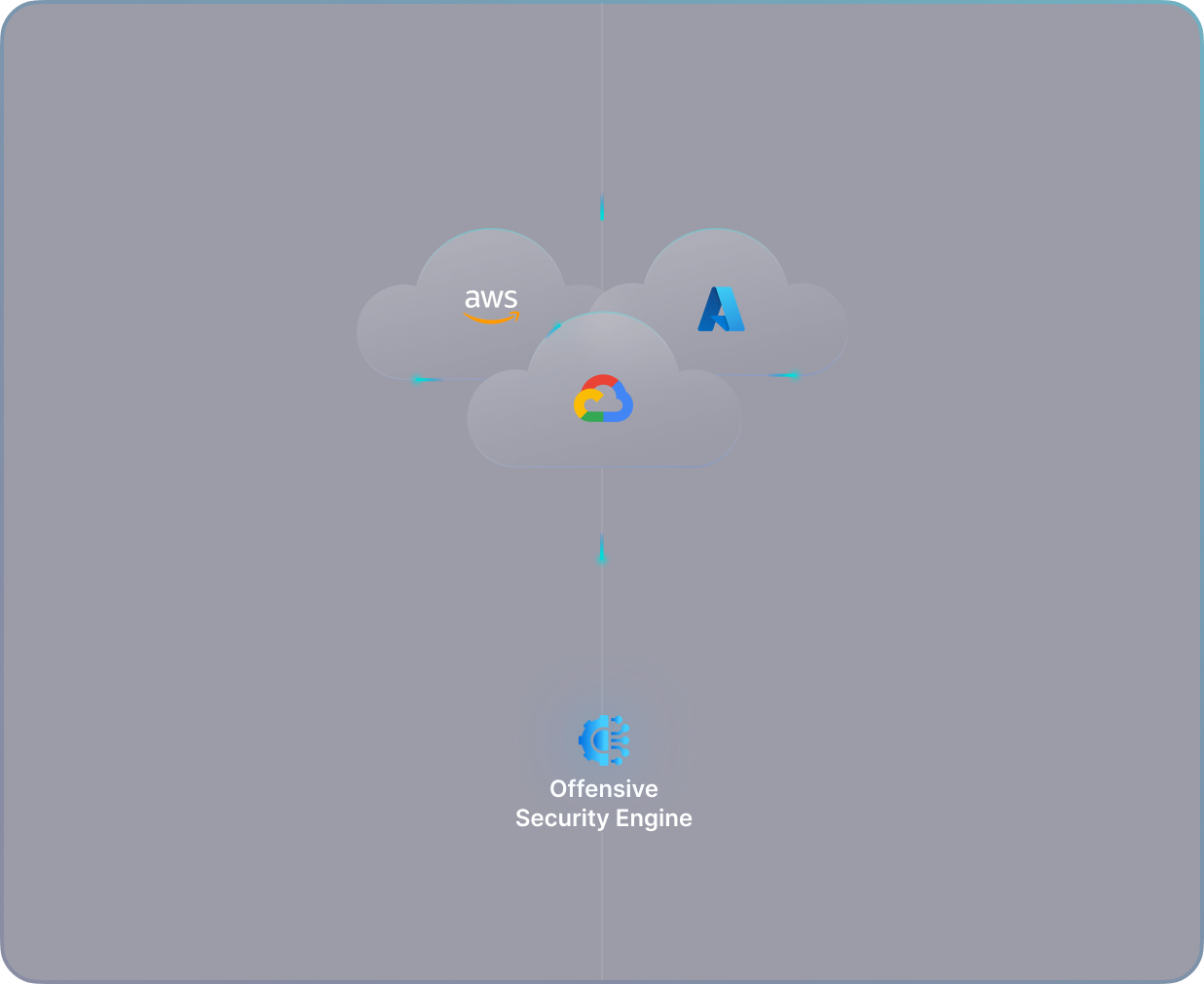
Discover vulnerabilities across your entire cloud infrastructure without installing any agent
Built by the team that has helped secure






Traditional agent-based scanners involve a time-consuming and complicated process for installation and maintenance. This becomes even more complex and costly as the size of your cloud infrastructure grows, resulting in a significant increase in overall cloud expenses.
Agent-based solutions are not able to provide a comprehensive view of configurations and identities across multi-cloud infrastructure, which can result in security gaps and blind spots. This can make it difficult to identify and mitigate potential threats, leading to increased risk for organizations.
Security teams relying on agent-based solutions become dependent on dev-ops and development teams for installation and maintenance, which can lead to increased workload and friction within the organization. This slows down the deployment process and hinders collaboration between teams, making it harder to secure the organization's infrastructure effectively.
Agents themselves can be vulnerable to zero-day vulnerabilities, which, If exploited, can put the entire organization at serious risk, potentially leading to data breaches and other security incidents.
You can get started in minutes. Our agentless approach requires just a few read-only access, and you start seeing results immediately post-activation of your account. This approach also ensures that you do not bear any additional cloud cost (which occurs in the agent-based approach) and are not exposed to any vulnerabilities in the agent itself.
PingSafe's scanning engine is designed to cover 100% of your cloud estate, eliminating any blind spots that could leave your organization vulnerable to security threats. This comprehensive approach ensures that every aspect of your cloud infrastructure is protected, reducing the risk of security incidents.
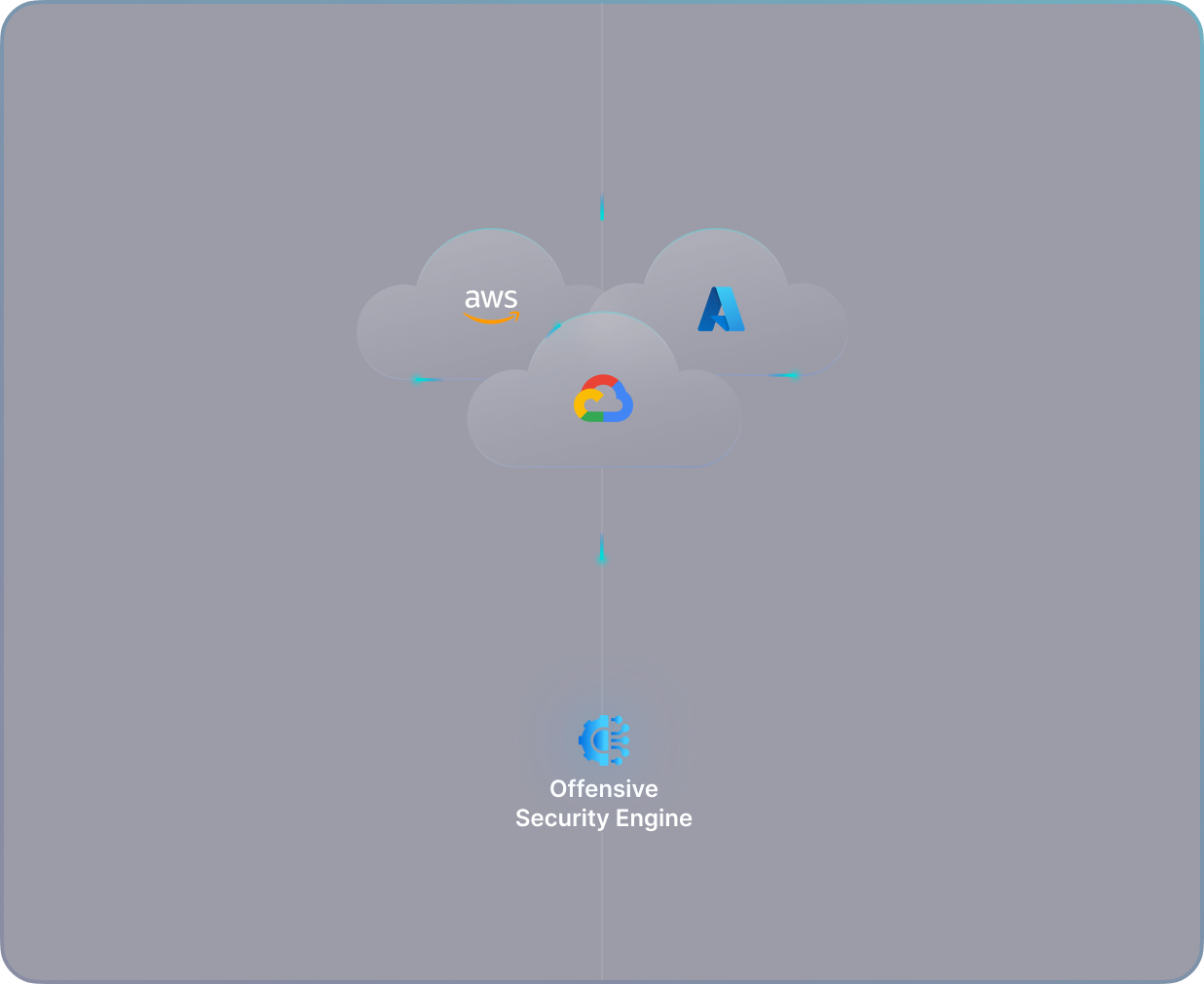
With the additional context of your workloads and misconfigurations, PingSafe's scanning engine can help to uncover dangerous attack paths that can result from seemingly unrelated and less severe issues. This allows security teams to identify and mitigate potential threats before they can cause critical consequences, improving the overall security posture of the organization.
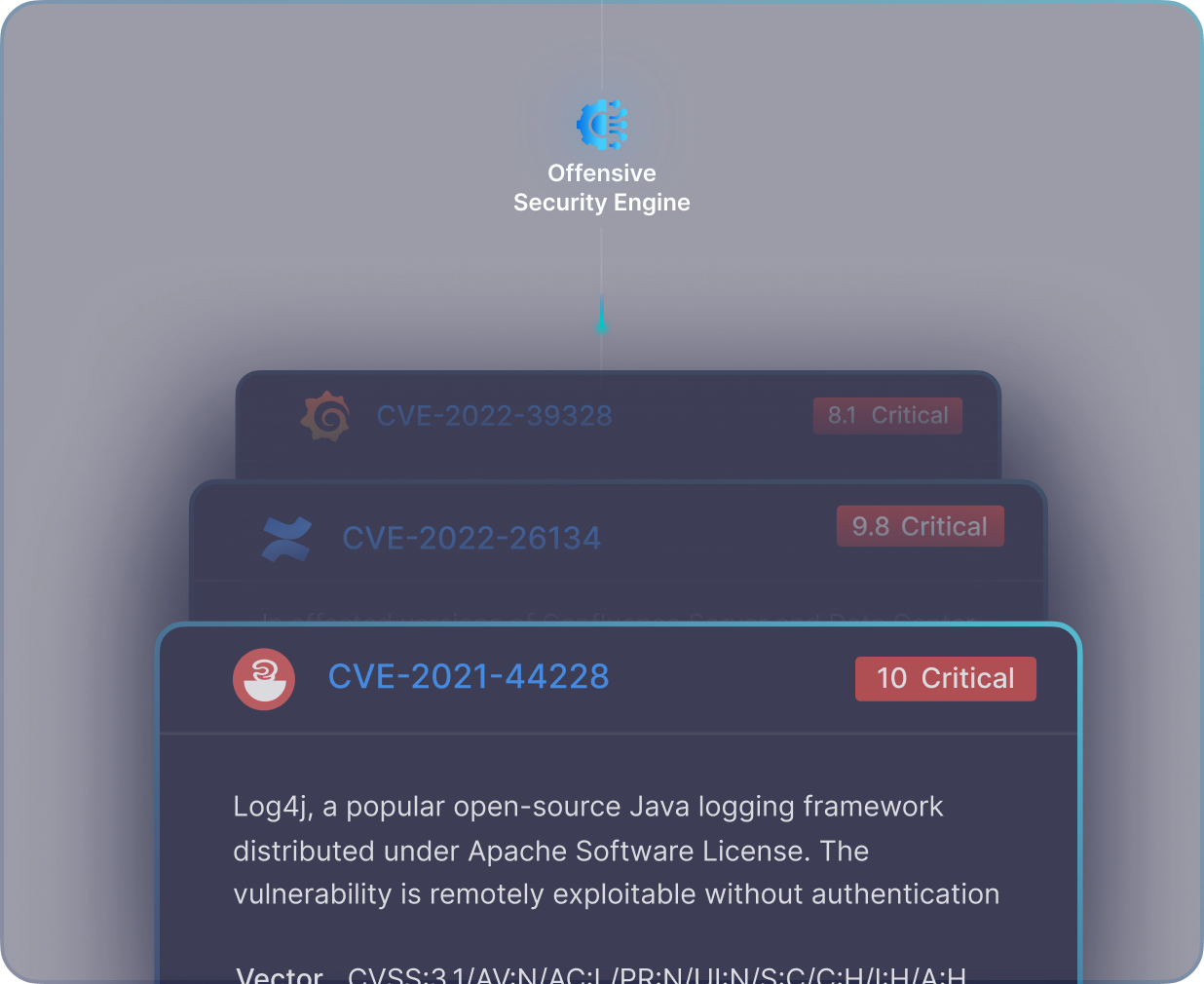
PingSafe's scanning engine is designed to uncover issues within minutes, allowing security teams to identify potential threats quickly. Our engine also prioritizes these issues, ensuring that the most critical risks are addressed in a timely manner.
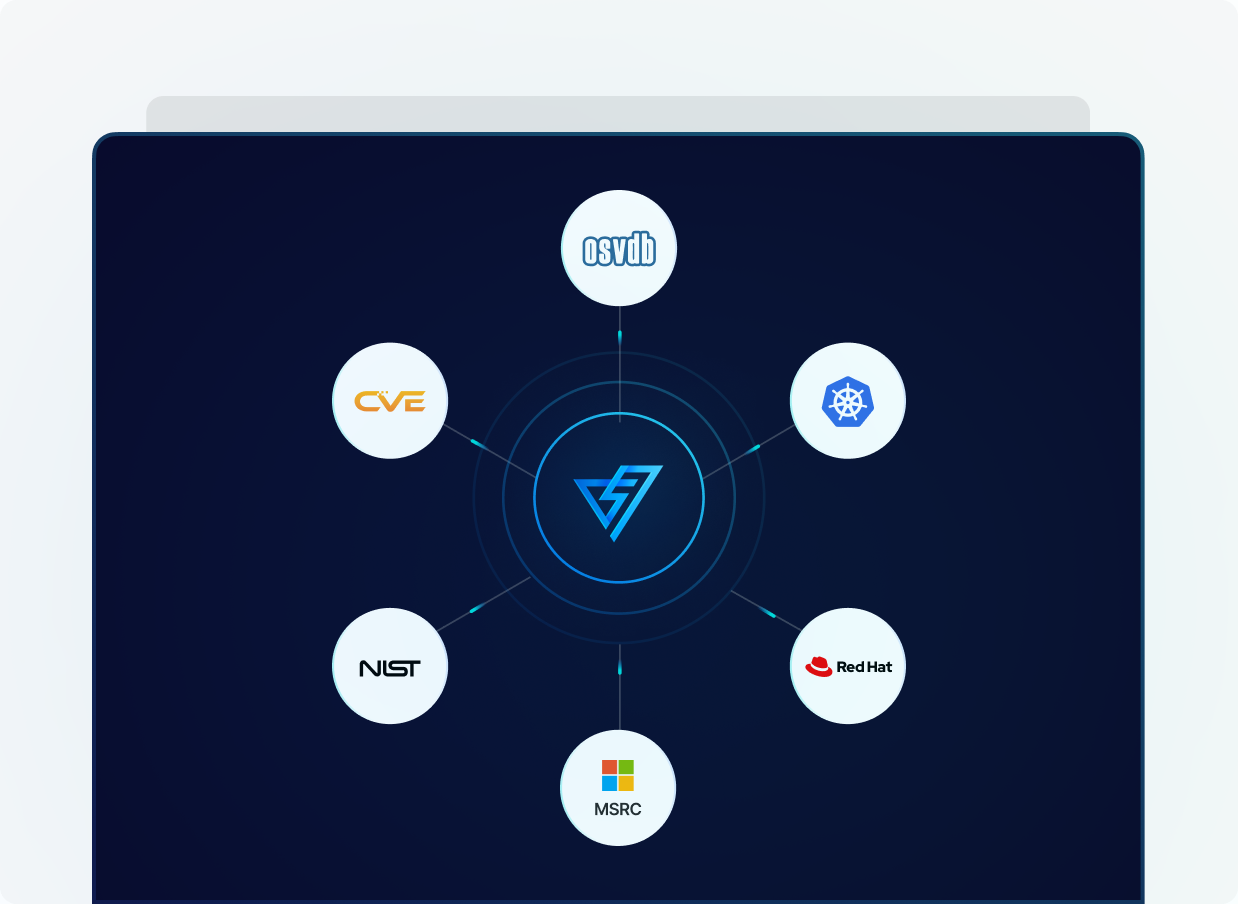
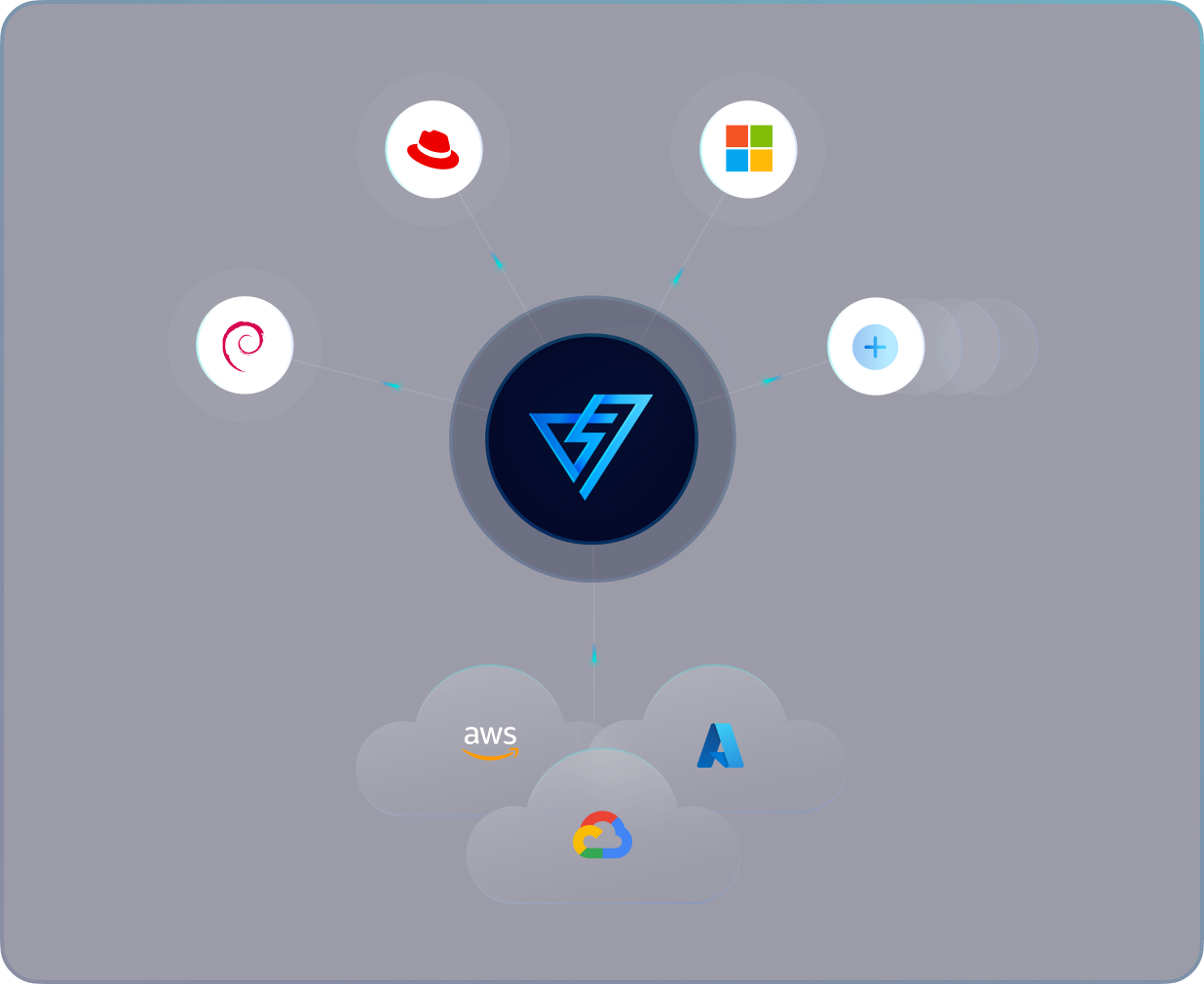
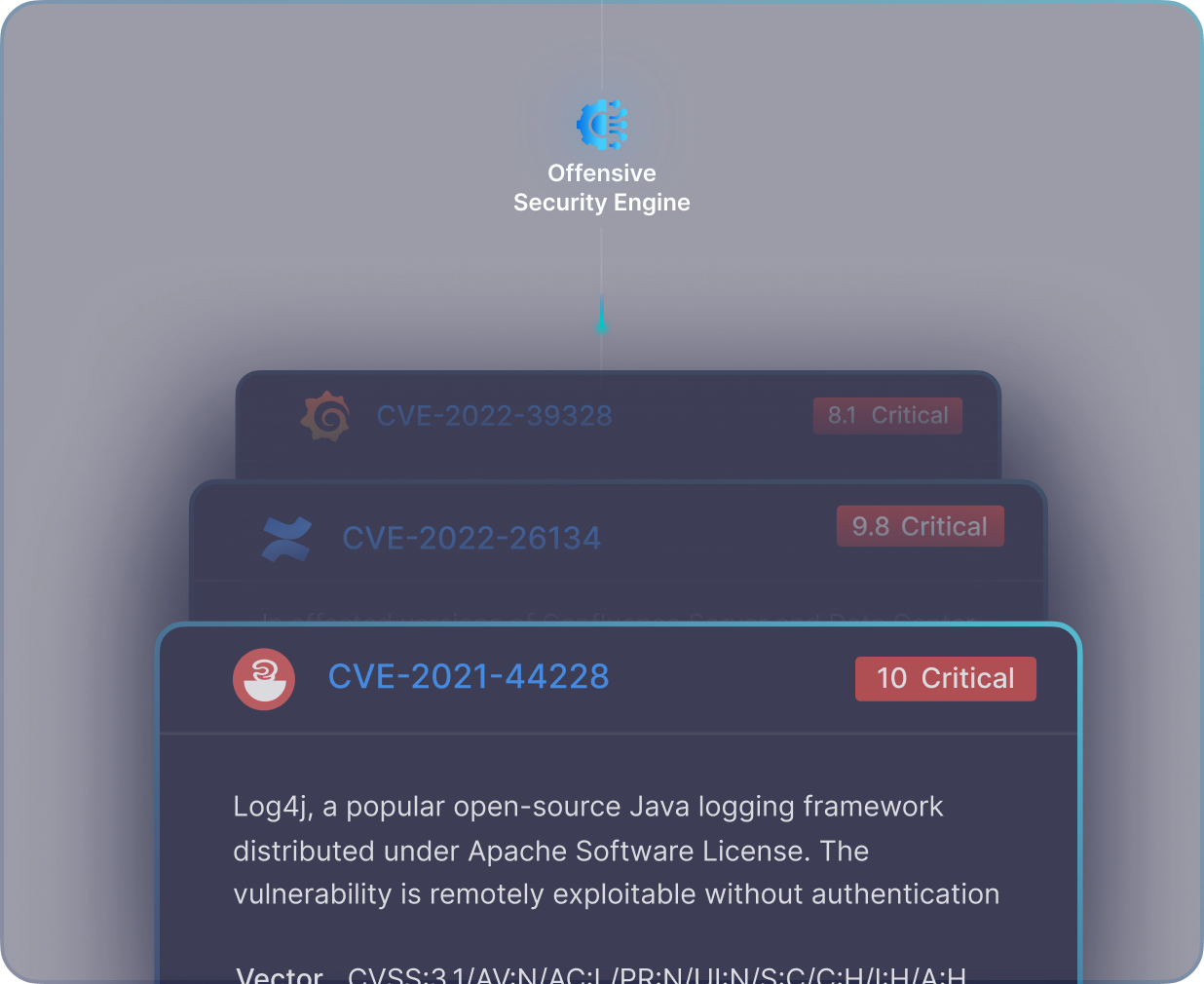
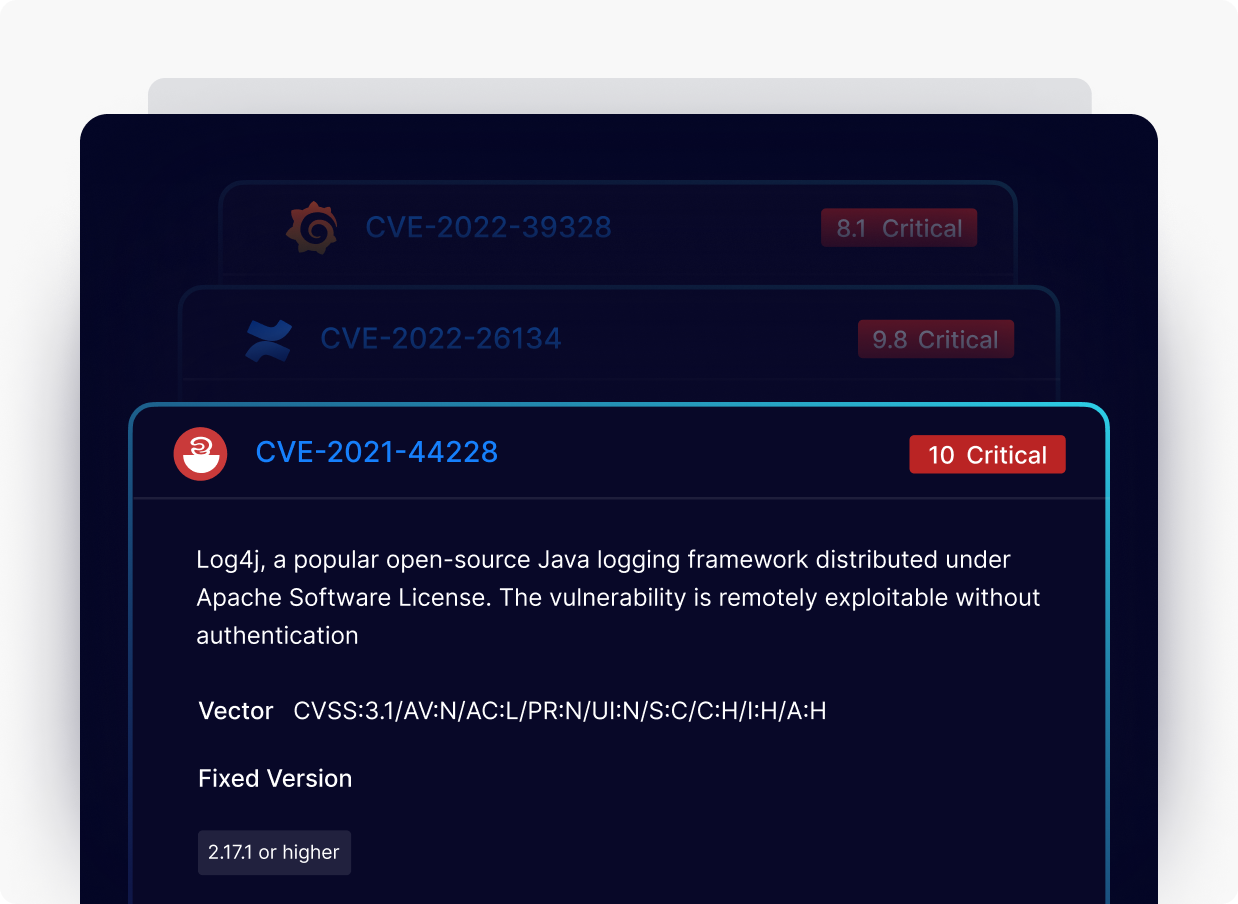
PingSafe's scanning engine uses a rich repository of known vulnerabilities from 25+ databases, including CVE, RedHat, NVD, MSRP, Kubernetes Security, OSVDB, and more. This ensures that organizations are safeguarded against new attack vectors, providing comprehensive protection for their entire cloud estate.
We provide evidence-based reporting of issues that are designed to provide possible attack paths/processes, to help organizations understand the potential impacts of vulnerabilities and their exploits and take steps to mitigate it. This detailed reporting can be used to improve the overall cloud security of an organization.
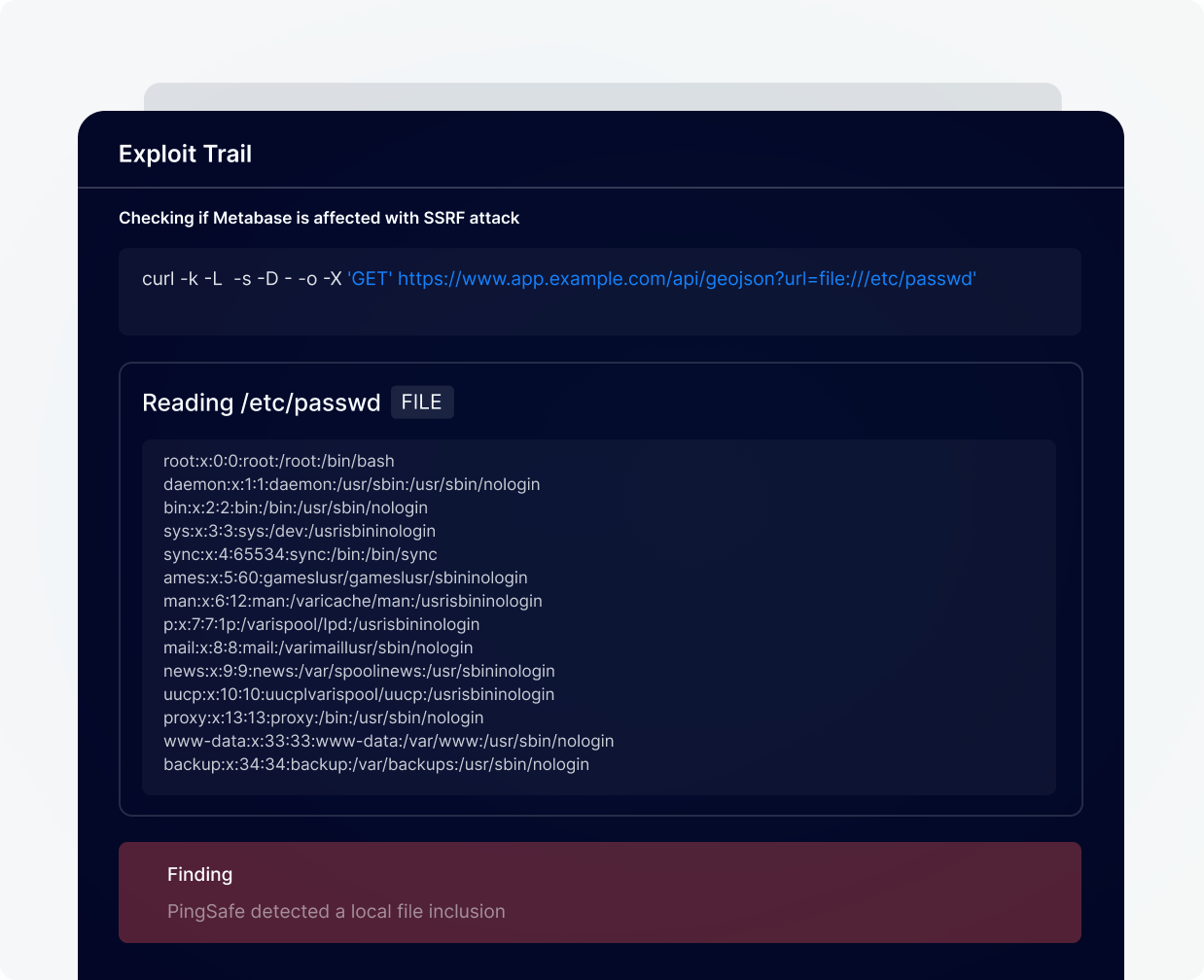
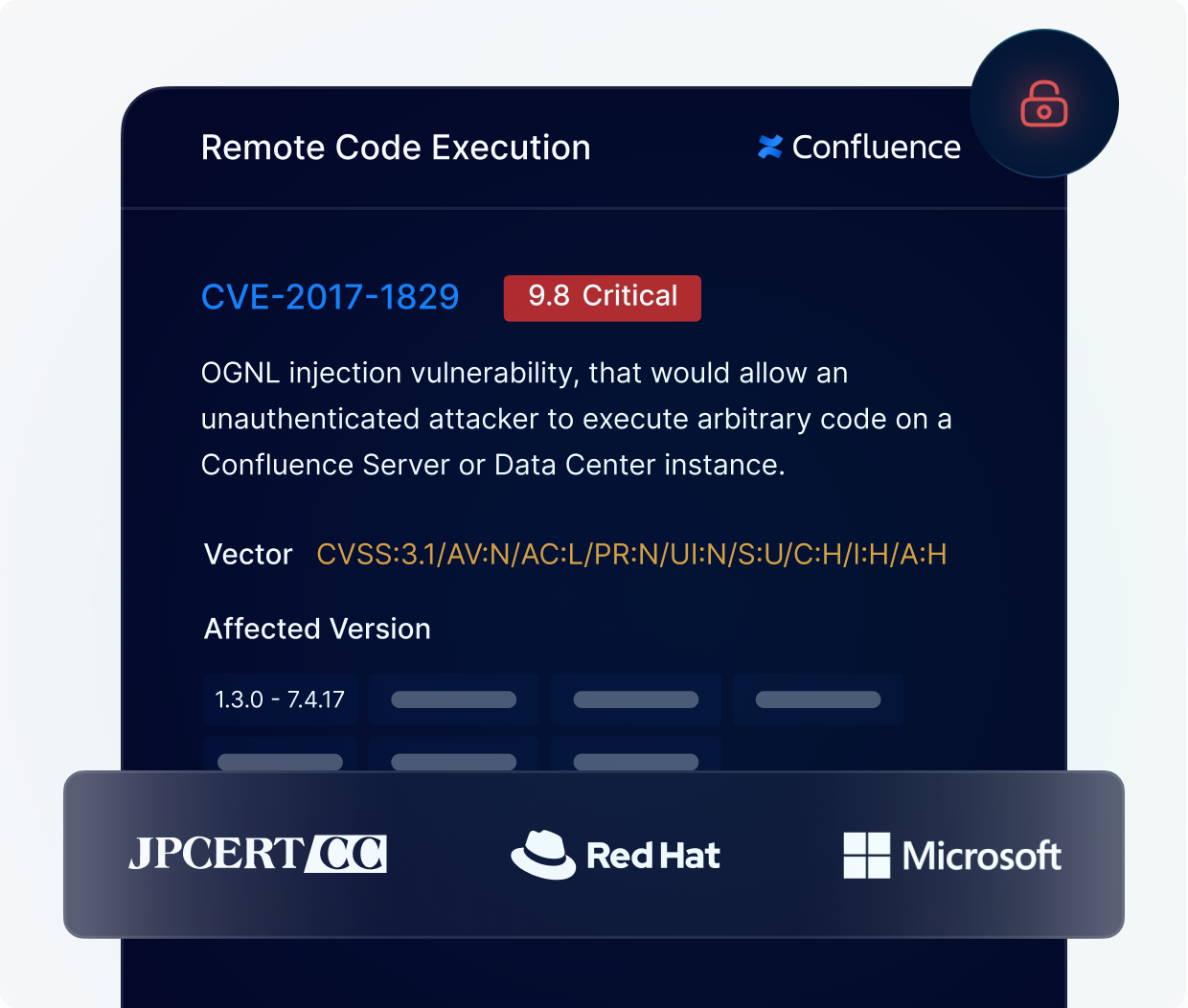
PingSafe's scanning engine provides contextual and prioritized reporting of identified vulnerabilities with zero false positives. This allows organizations to focus on the most critical issues and take action accordingly. With a zero false positive rate, you can have confidence that identified vulnerabilities are genuine and require attention.
Our solution is designed to provide a single view of all vulnerabilities across your entire multi-cloud estate, allowing you to manage and address security risks in one central location. This comprehensive approach ensures that every aspect of your cloud infrastructure is covered and protected. With a single view of all vulnerabilities, you can quickly identify and prioritize the most critical risks based on your organization’s business and security objectives.
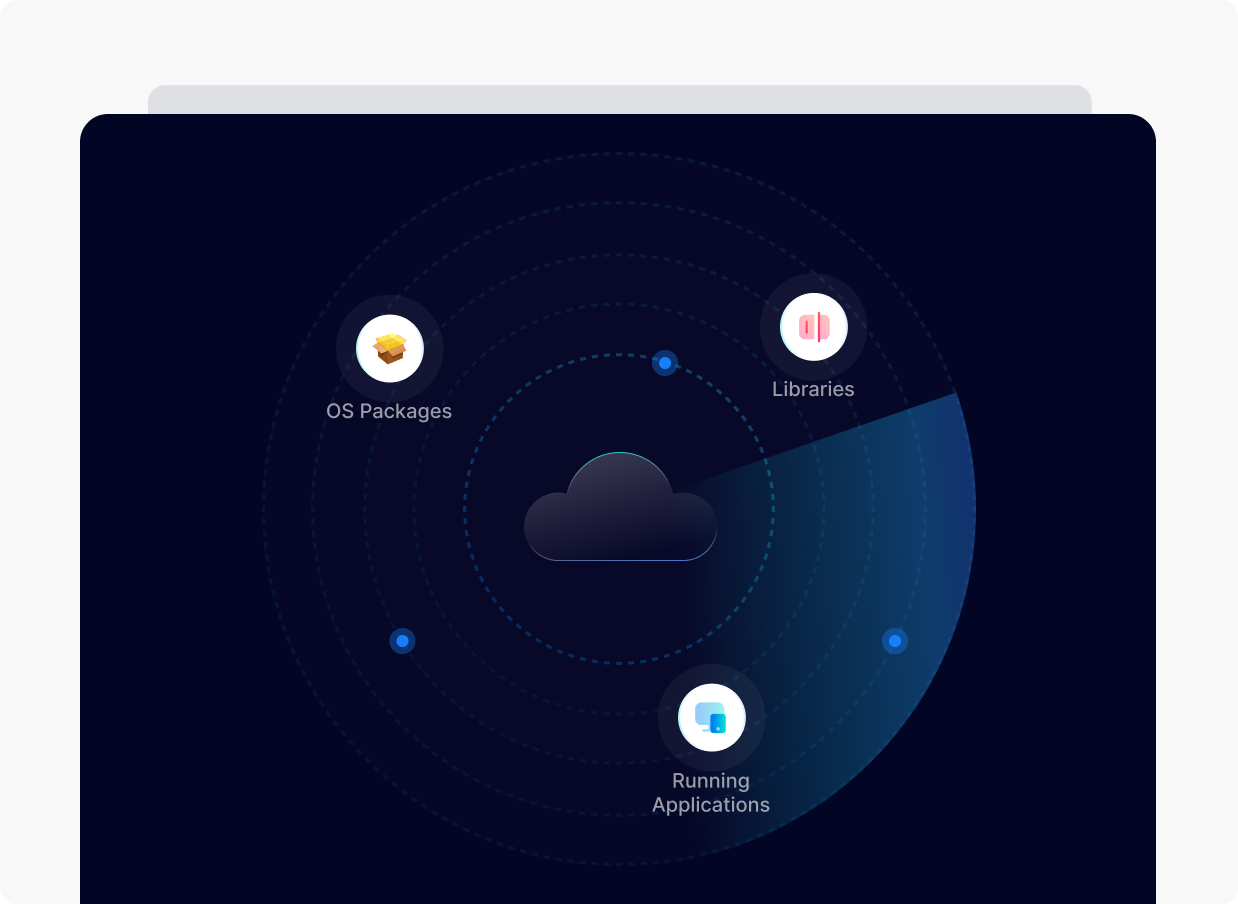
Our solution continuously assesses and monitors your cloud workloads to help keep your infrastructure secure. This includes regular checks for vulnerabilities in OS packages, libraries and running applications, and identifying potential security risks. By continuously monitoring your workloads, our product helps you identify and address issues quickly, ensuring that your systems remain secure at all times.